We are in an age where AI is cranking out content faster than you can say “Blade Runner”, promising businesses a brave new world of efficient and on-point messaging. But while AI generated content has its merits, the jury is still out on whether robots can really replace the nuance and creativity of humans.

Sure, AI can write, but can it feel? The authenticity, the raw emotion, the individual flair that a human writer brings to the table is irreplaceable. Businesses gunning for a personal connection with their customers might find themselves swimming in a sea of sameness, with AI-generated content that sounds more generic bot than brand ambassador.
Copying homework is not just a problem for students. AI, despite its prowess, isn’t above accidentally nicking someone else’s work. And let’s be real: a lawsuit for copyright infringement isn’t the kind of publicity any business is chasing.
Want an article on climate change? AI’s got you. Want one that understands the heartache, struggle, and grassroots activism behind it? Maybe not. When businesses spout content that feels out of touch, it’s a fast track to “cancel town” for ignoring the cultural nuances of their clientele.
Testing AI Detector websites with Standardized Pricing per 1,000 words
We’ve tested the top AI Content detectors so you don’t have to. Keep a sharp eye on the pricing because you will quickly rack up a bill for these tools. Some are way more effective than others. Our tests were made with the identical article, so you can see how the results will work.
The clear winner of our test is Easy AI Checker. With an integrated plagiarism check, speed, a fix system, and a generous 6,000 word per day limit, this website will be an affordable and useful tool.
In order to standardize pricing, we assume that the average word is 8 characters.
1. AI Content Detector (copyleaks.com)
Long the industry leader for plagiarism checking, their AI detector overall does better than any other free tool. Copyleaks offers the highest quality AI detector and plagiarism checker.
You can freely test it. We never ran into a daily limitation, although there is supposed to be one.
The main complaint is the output screen size. If you test a longer article, the screen only shows a snippet. If you are screen-shotting it to send it as proof to your instructor, only about 10 lines of your text will show in the detector.
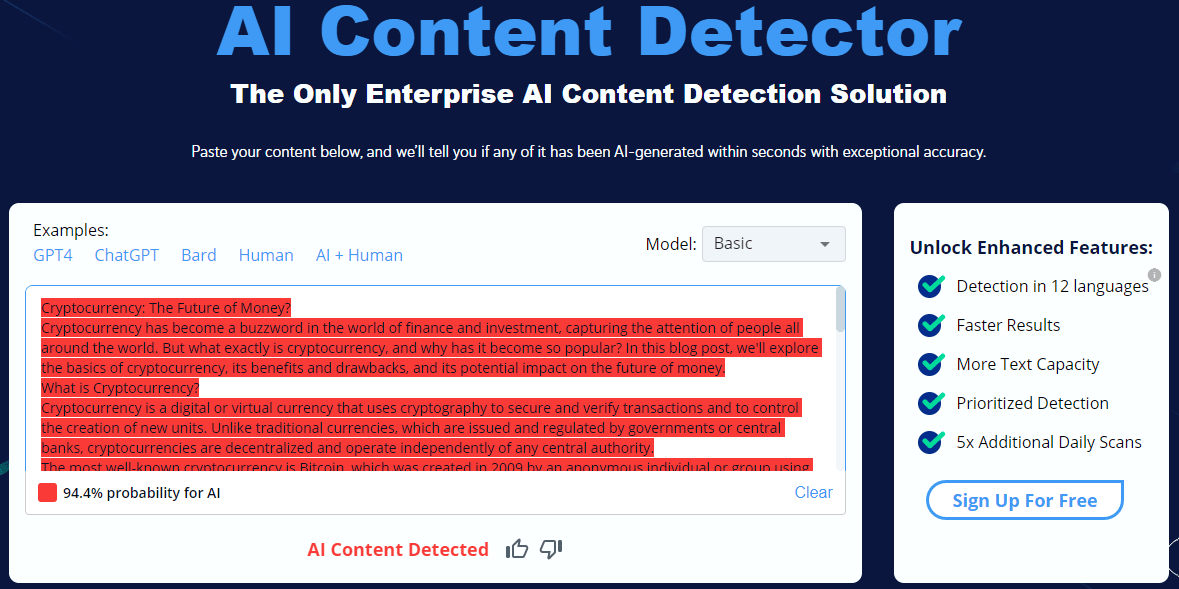
When we entered our standard text which was AI generated, they accurately detected it. The readout is very simple and does not show any nuance. The formatting of our text was not retained.
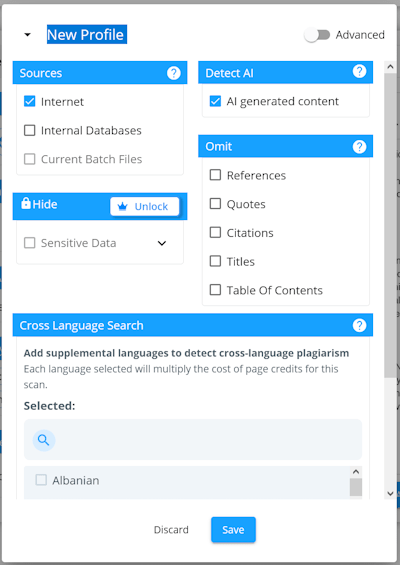
While we were writing this article, Copyleaks changed their interface an it looks like they require an account just to do a basic check. A free account is 10 Pages with a note that a page is 250 words. The interface is very complex, requiring you to select multiple options. You cannot scan for AI without also doing a plagiarism check. For our test it took 2 minutes to scan 200 words.
Their tool did detect AI generated content, missed some items that were AI generated. Overall this is an expensive and cumbersome tool that forces you into a large set of options for a simple task.
Features:
- Chrome Extension
- Plagiarism Checker
- AI Grader
- Customizable API
Pricing:
- Account is required to test, gives 6250 words forever
- $11 per month for 25000 words ($0.44 per 1000 words) places this among the more expensive ones we tested.
2. AI Detector Free (EssayPro.com)
EssayPro AI detector is a valuable tool that helps you determine whether your text has been generated by an AI. This AI text detector uses sophisticated algorithms to analyze your content and highlight any areas that seem AI-written, providing you with a clear breakdown of the findings. The tool is known for its efficiency and accuracy, making it a great option for anyone concerned about the originality of their work.
One of the standout features is that you can use the AI detector free of charge. There’s no need for a subscription or additional fees to scan your text for AI-generated content, which is a significant advantage for users on a budget.
If you’re looking for a free AI detector that can handle various AI models like GPT-4 or Copilot, EssayPro’s tool is worth considering. It offers a straightforward interface, easy-to-understand results, and the convenience of being able to check your work as many times as you like. Although no tool can guarantee 100% accuracy, this AI detector remains a reliable option for ensuring the integrity of your content.
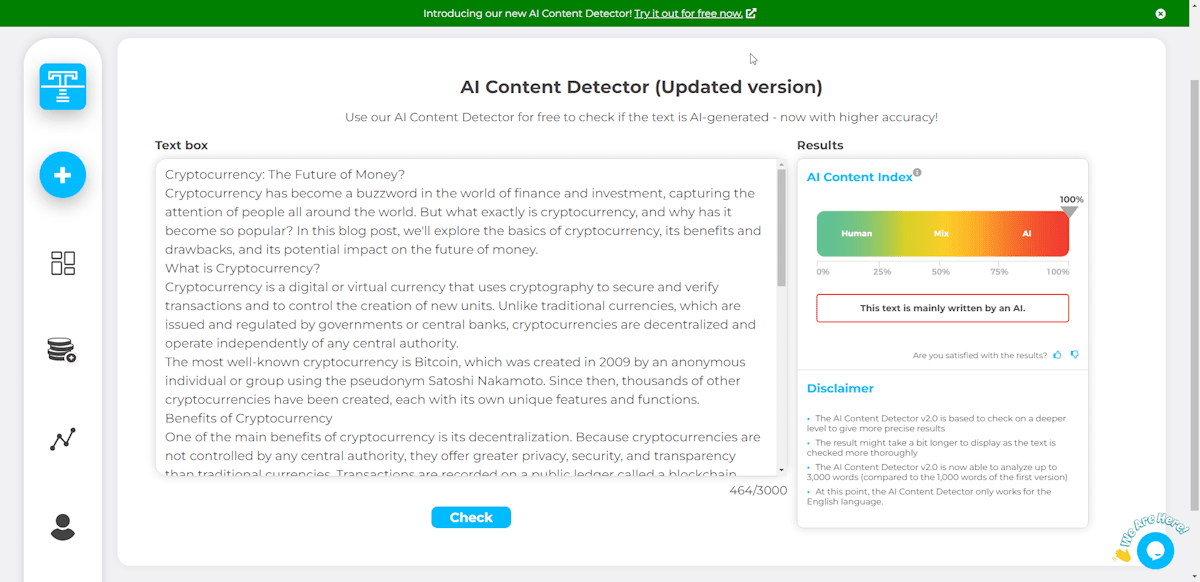
3. AI Content Detector (writer.com)
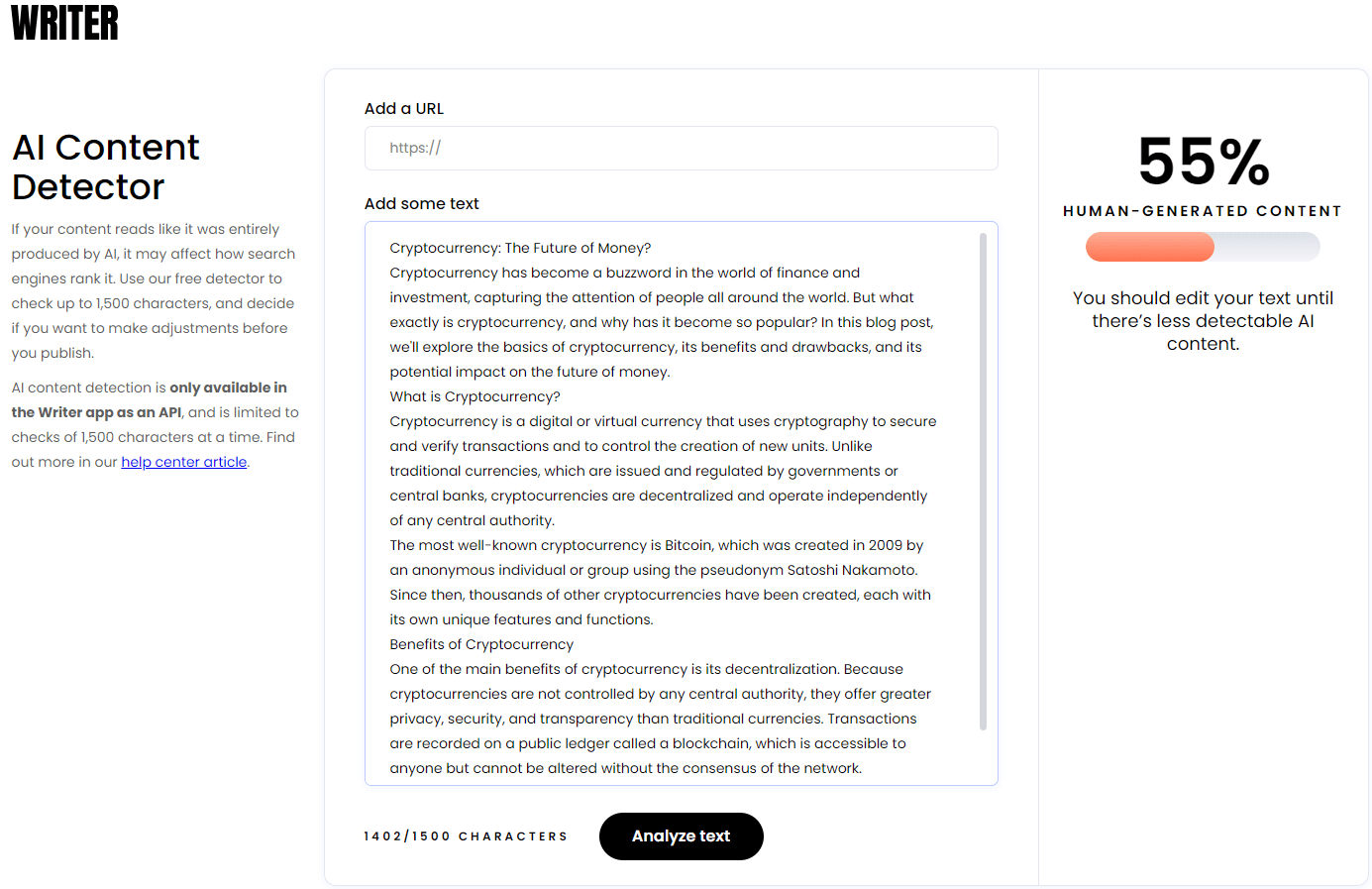
Writer’s AI Content Detector is minimal, with no document upload or options to maintain formatting. A simple text box and a URL option is all that Write’s AI checker offers. Using the same test article which was 100% AI generated Writers’ checker only found about half of it to be generated. Keep looking if you want a Checker with decent features and a better detection rate. The trial is limited to about 150 words which is too short to really test it.
Pricing:
- 200 words Free
- 15,000 words – $18 per month ($1.20 per 1,000 words).
4. Scribbr AI Detector
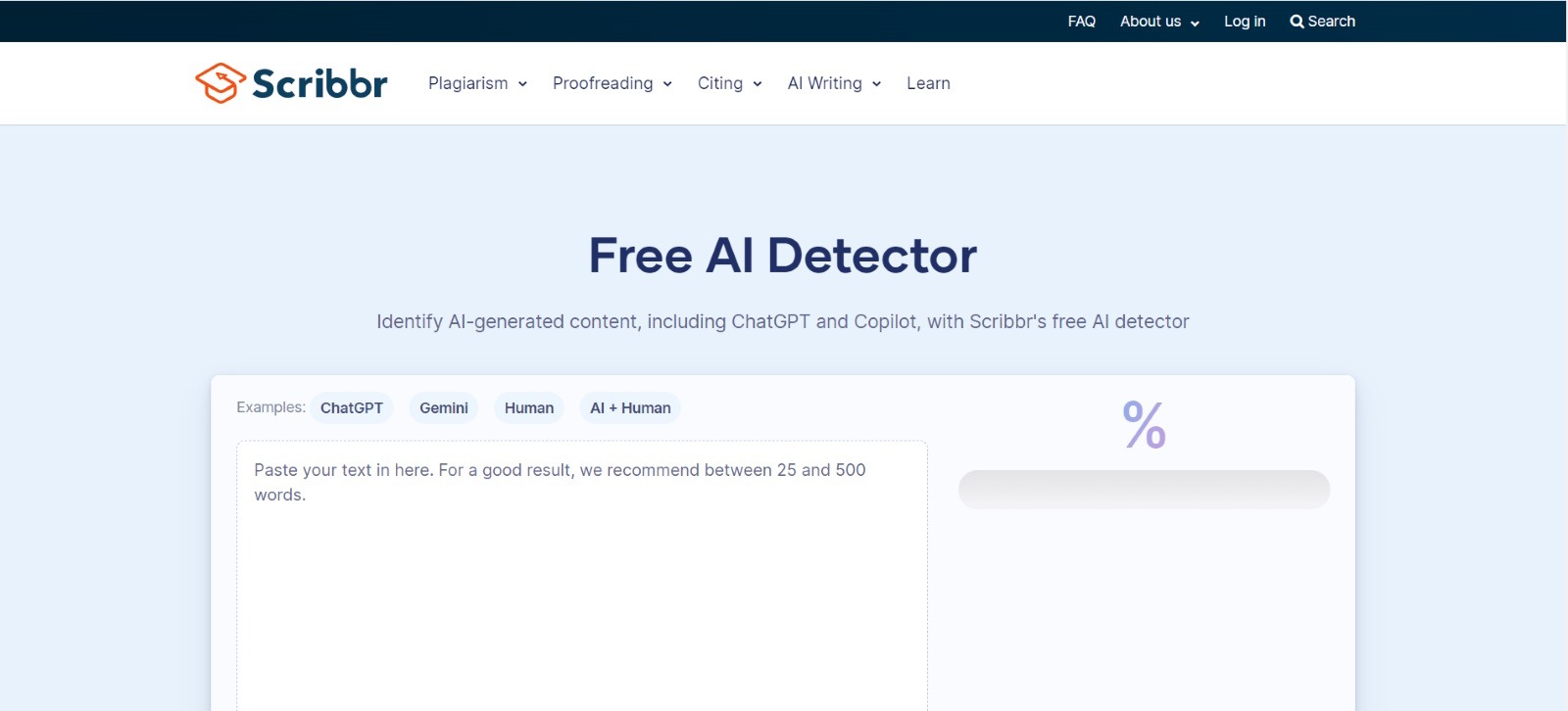
Scribbr is another widely used AI content detector, which can detect content written using different AI models, including GPT4, Gemini, Copilot, etc. The tool is completely free and allows users to scan text an unlimited number of times. It uses advanced AI algorithms to detect patterns that make a text look AI-written and highlight the suspected part.
You can check a maximum of 500 words at once, but there is no restriction on the number of times you can run the check. Although no tool can be 100% accurate, Scribbr is among the most accurate AI detectors.
Pricing: Scribbr’s AI content detector is 100% free. There are no charges applicable for scanning text and detecting AI content in it.
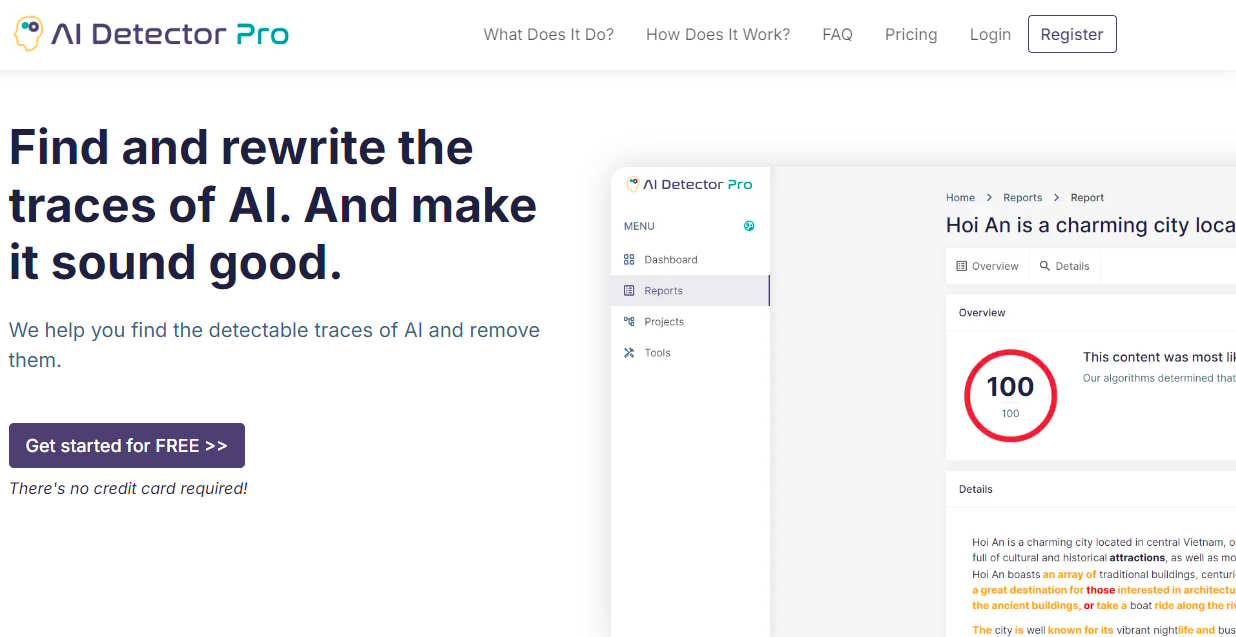
5. AI Detector Pro (aidetector.pro)
AI Detector Pro is a combination of an AI Detection and Writing platform.
Simple detection and humanization platforms ignore a key element of AI content: that AI writing sounds robotic to the human ear. Whether or not you pass detection, your writing may not pass muster when read by a human, and you may still be accused of cheating, or passed over for a contract. This is why AI Detector Pro added editing features to their advanced detection technology, so you content creators make their writing sound more human whilesimultaneously checking whether they passed other detection programs. Their features include AI Detection, Google Sheets & Word Plugins, an AI Tone Mapper, Auto Re-write, AI Dictionary, and AI Phraseology. While you can view every feature in their 3 Free reports, you must upgrade to a Paid Plan to use their advanced features. Learn more at aidetector.pro.
6. Easy AI Checker (easyaichecker.com)
Easy AI Checker offers several unique features that made it our favorite. The AI check is lightning fast, free and does not require a login or captcha. The integrated plagiarism check worked when we tried it. It is one of the few tools that took URL input, and the only tool with PDF output. There is even a remarkably effective AI Fixing tool to fix the AI detection of your text.
Formatting of entered text is maintained and it correctly and totally identified a fully AI generated article. With Reasonable Pricing and Advanced Features Easy AI Checker is one of the top choices for Checking and Correcting AI content.
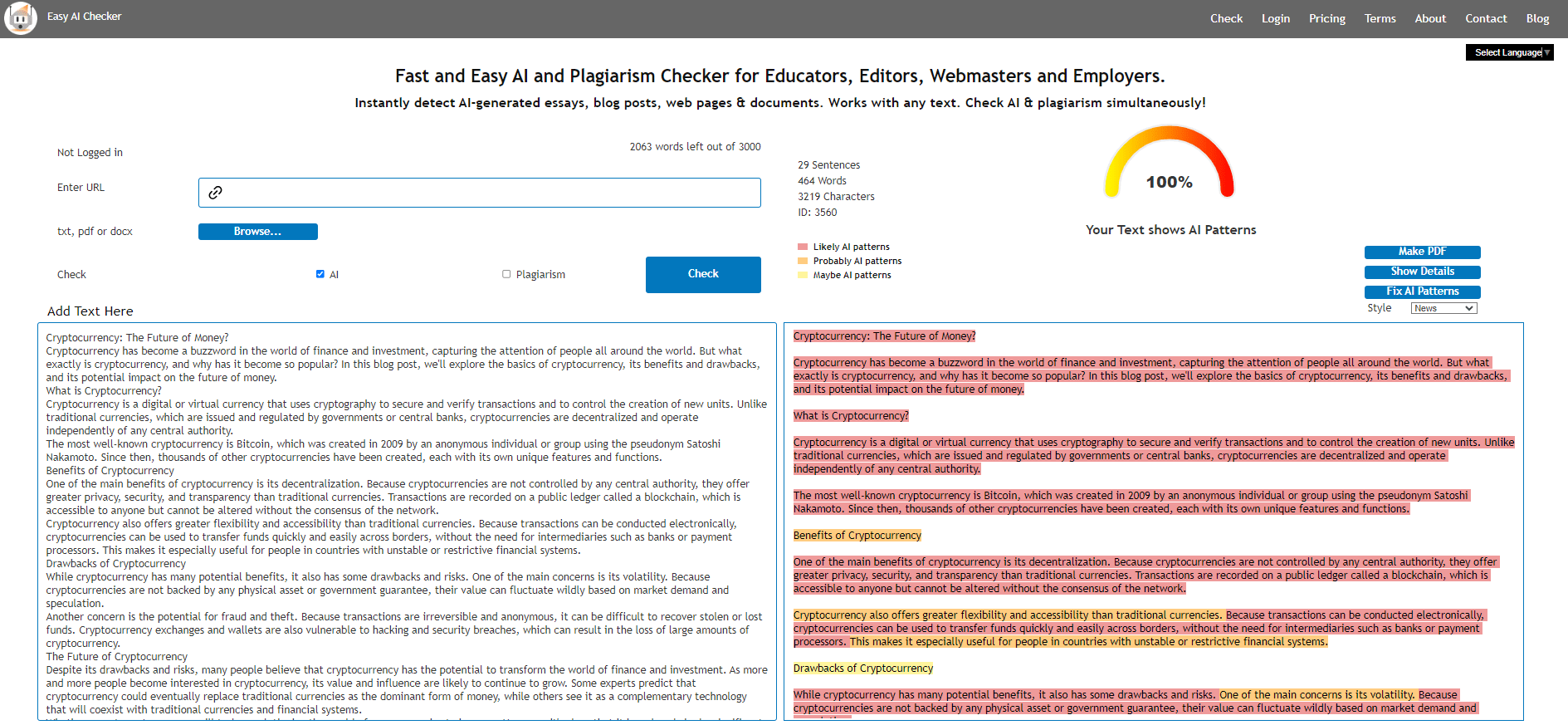
Features:
- The only tool that can check Plagiarism at the same time as AI
- The only tool that produces a PDF report
- URL entry, Document entry
- Integrated AI Fixer (humanizer) that clears the AI patterns.
Pricing:
- 6,000 Words per day with login.
- 20,000 Additional Words: 12$
- 100,000 Additional Words: 12$ Monthly ($0.12 per 1,000 words)
- 1,000000 Additional Words: 100$ Monthly ($0.10 per 1,000 words)
7. Free AI Detector (scribbr.com)
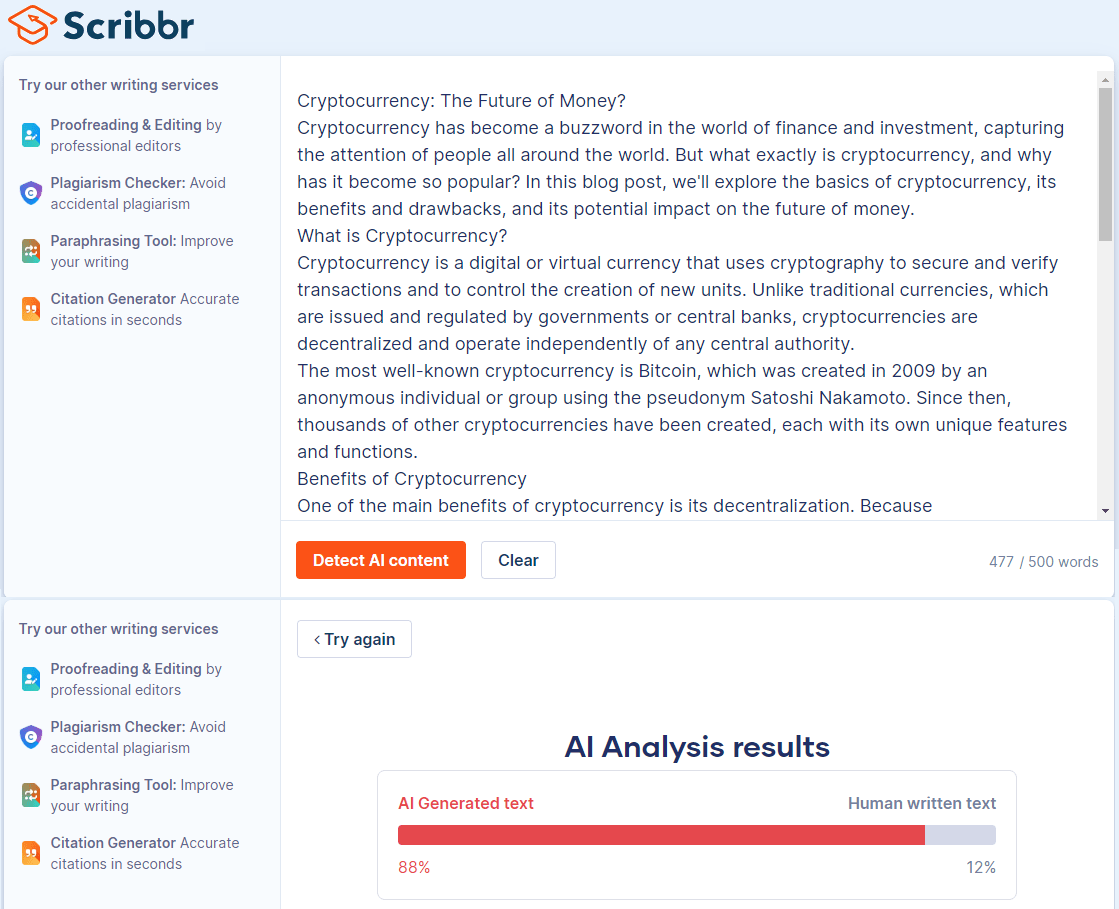
Scribbr’s AI Content Detector is also very minimal, it has no document upload, URL entry, or options to maintain formatting. A simple text box is all that is offered by Scribbr’s AI Detector. Using the same test article which was 100% AI generated Scribbr’s Detector only found about 2/3 of the article to be AI generated. Keep looking if you want a Detector with any features and a better detection rate. It is fully free but very limited to 500 Words at a time, so a normal article will take at least two tests.
In our testing, Scribber was the most minimal and by far the most expensive solution.
Features:
- Plagiarism Checker (with account)
- Paraphrasing Tool
Pricing:
- 500 Words: Free
- $19.95 for 7500 words ($2.66 per 1,000 words)
8. Quillbot
QuillBot’s AI Detector tool is a free tool designed to identify AI-generated content from platforms like ChatGPT, Gemini, and Claude. It distinguishes between text created entirely by AI and text refined using assistive tools such as paraphrasers or grammar checkers, aiming to reduce false positives and cultural biases. The detector provides detailed analyses, highlighting specific portions of text that appear AI-generated, and delivers results quickly.
9. GPTZero
GTPZ offers a decent AI Text Checker. While it did properly detect some AI generated content from the sample document their UI only offered a “Likely to be written by an AI” result. It seems their more advanced features like highlighting the text that was detected as AI and a batch upload option are locked behind their Premium Account
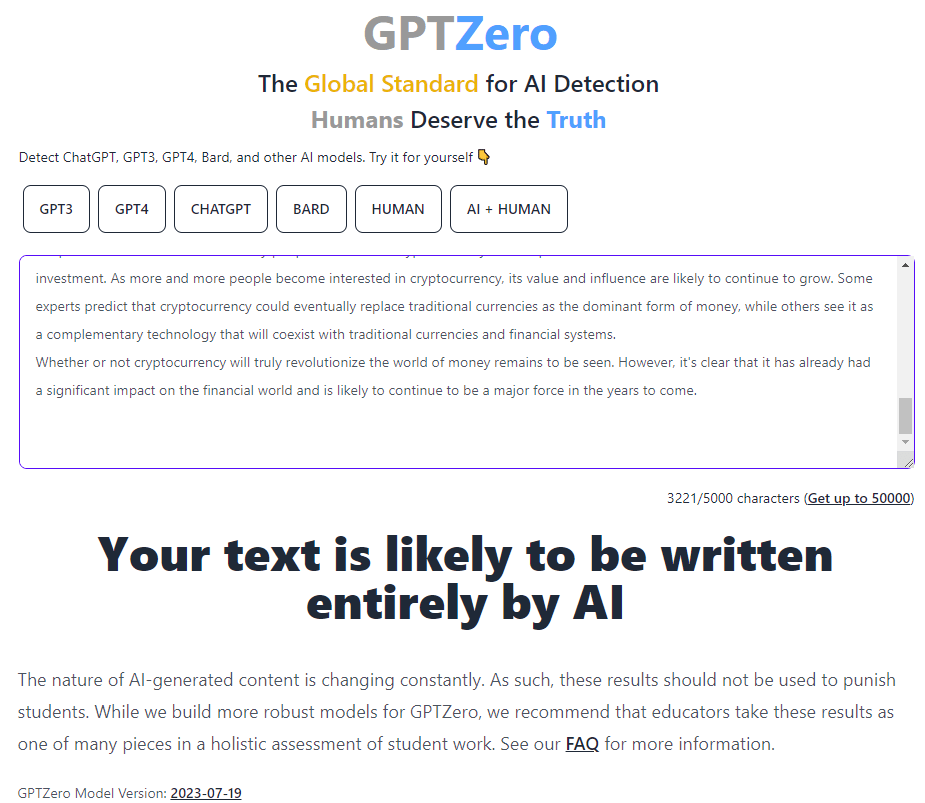
The Formatting of the uploaded article used for checking was decently maintained. GTPZero has some nice features, but there most are locked behind a premium account.
Features:
- Batch Upload (Premium Account)
- Detailed info on what was detected as AI (Premium Account)
- Chrome Extension
- API Access
Pricing:
- 1500 words Free
- 1,000,000 words – $9.95 per month ($0.01 per 1,000 words)
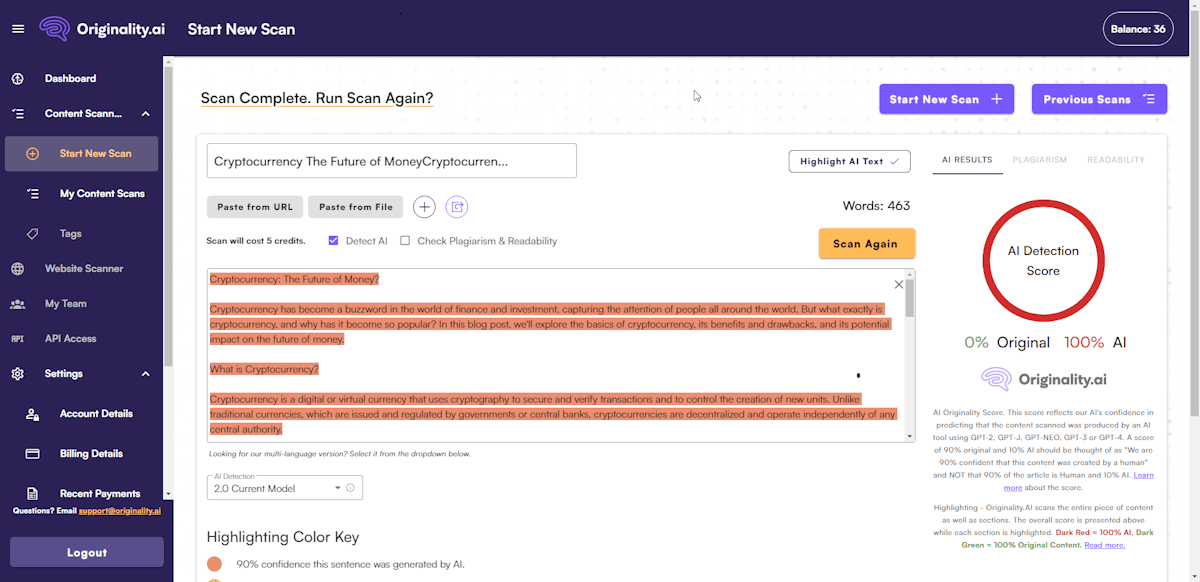
10. Originality.AI
Billed as the Most Accurate detector, Originality AI also was the most difficult for us to test.. You cannot test without a login. Creating a login took us three days and an email to tech support. Their Chrome add-in did not work for us. The Chrome add-in requires email and password for every useand does not auto-fill it.
No free trial. The cost is not bad, about $0.30 for 1000 words.
To be fair – they claim to be more accurate.
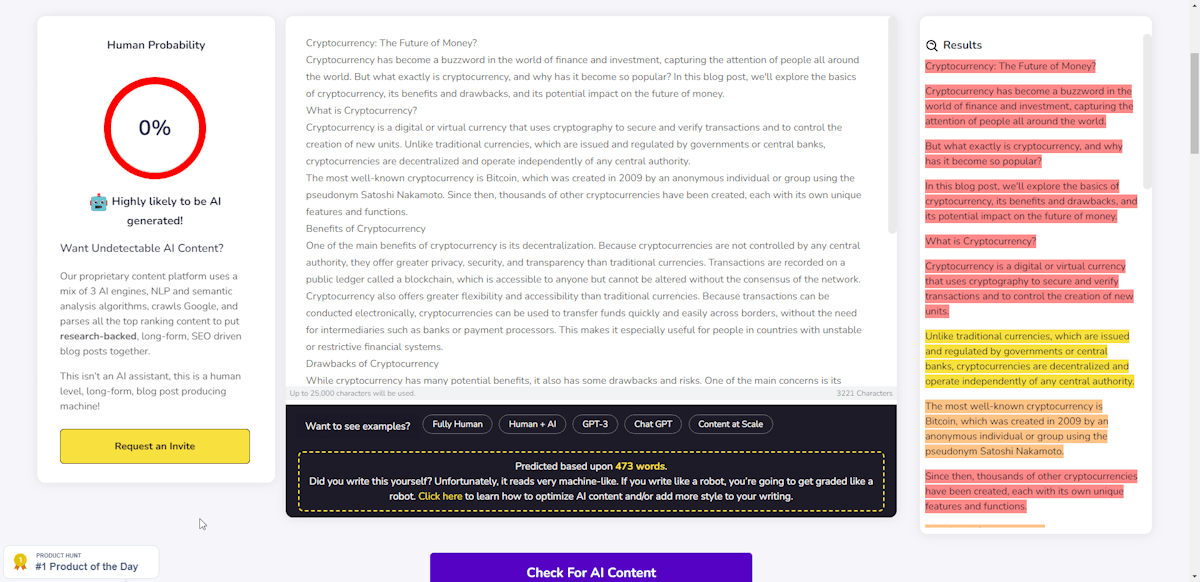
11. AI Detector for ChatGPT (Content at Scale)
The folks at Content at Scale are focused on another task – producing AI-generated content. But they provide a free AI Checker that is pretty decent. It will check up to 25,000 words. It is not the fastest that we checked. But it is the only one that is completely free.
12. Crossplag
This tool requires a login to be used. However, checking is free. You can check up to 3,000 words at a time.
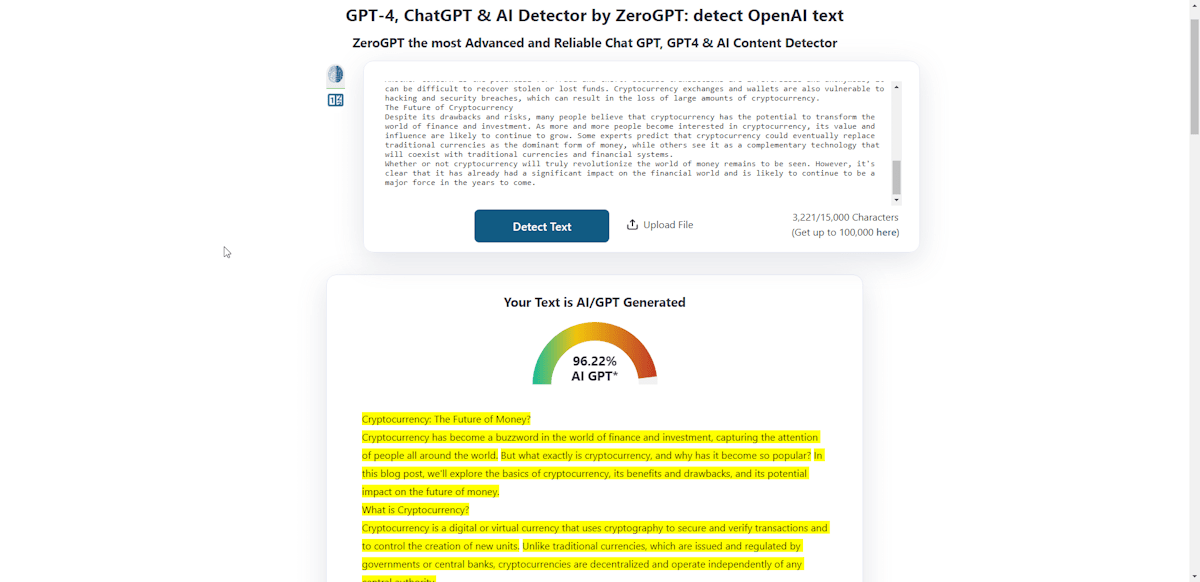
13. ZeroGPT – (zerogpt.com)
A simple AI checker with no plagiarism check. ZeroGPT has a very generous word allowance of 15,000 words per day (about 20 articles).
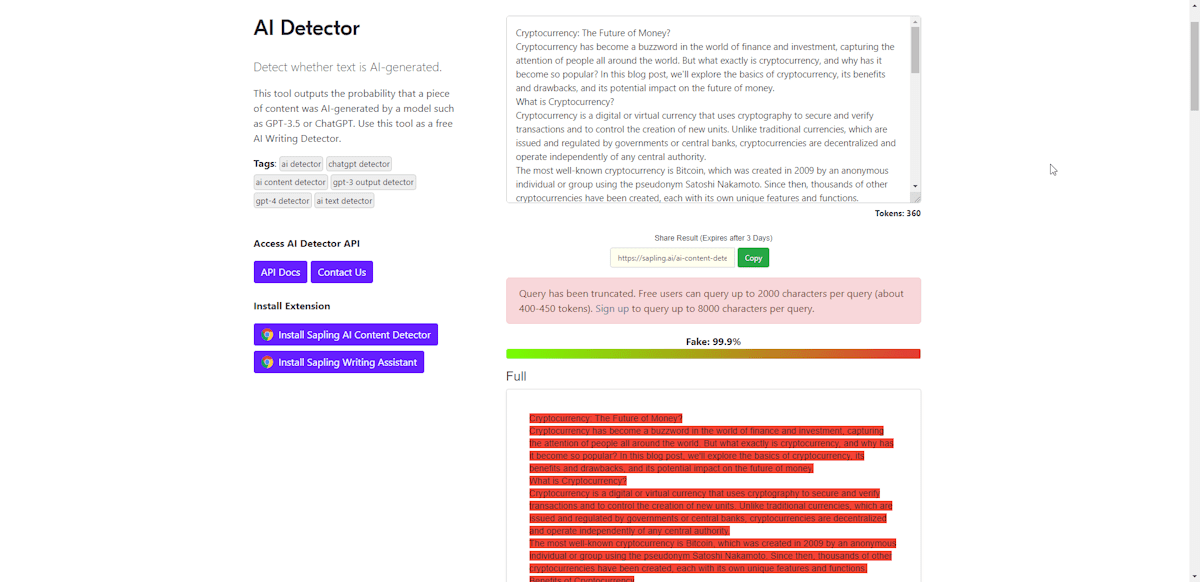
14. Sapling Content AI Detector –
For sheer confusion, the pricing of Sapling cannot be beat. AI detection appears to be on the “Pro” plan for $25 per month, and the API cost resolves to about $0.25 per 1000 words.
15. Smodin –
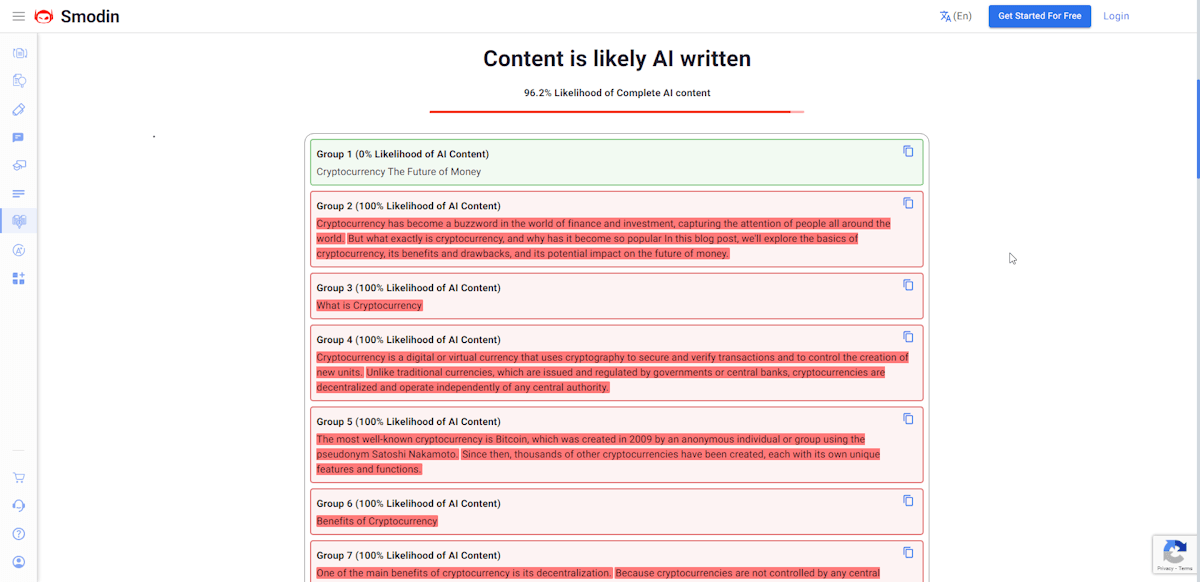
The last tool we tried was Smodin, Free AI content dector which correctly identified our text as AI written. Smodin says they work in 24 languages. Their 5000-character limit, and captcha requirement mean this free tool will cost you more time than needed. But hey, maybe you like to fill in captcha’s all day so this may be a good tool for you.
Conclusion
AI-generated content may seem innovative for businesses to engage with their customers, but it comes with many challenges. While AI can speed up the content creation process and make it more efficient, it can also be detrimental to a business’s brand reputation and voice. Thus, businesses must think carefully before embracing AI-generated content, considering its advantages and drawbacks, before using it in their engagement strategies.